The end of simple bots? How AI orchestration is revolutionising automation
Business process automation as we knew it is becoming a thing of the past, with simple bots that…
How AI is quietly changing purchasing departments
A quiet revolution is underway in purchasing departments, driven by artificial intelligence, which is transforming them from cost…
The clock for Windows 10 is ticking. Companies face an inevitable decision
In less than a month, on October 14, Windows 10 will lose critical security support, exposing millions of…
ISO 27001 certification in the supply chain: Trust or verify?
In digital business, a partner's ISO 27001 certification is often treated as a guarantee of security. However, without…
Microsegmentation 2.0 – how to effectively protect a network without agents
As IT infrastructure becomes increasingly distributed and dynamic, traditional methods of network protection are becoming less effective, forcing…
AI FOMO: Why are companies investing in AI out of fear rather than strategy?
Artificial intelligence has become a technological imperative, forcing companies to invest frantically so as not to fall behind…
Technology giants’ slip-ups. What can we learn from the biggest failures in the IT world?
Silicon Valley is home to a graveyard of brilliant ideas and products that were supposed to change the…
AI in sales will not replace the salesman. It will make him a superhero
Contrary to fears that AI will automate sales, its integration with CRM systems is proving to be the…
Shadow IT: Enemy or unwanted ally? How to use it for innovation
For years, the traditional approach to data security forced companies to make an unfavorable trade-off between robust protection…
Cloud in Europe: Between US dominance and the fight for data sovereignty
European business, driven by innovation and scalability, relies heavily on the cloud services of American hyperscalers. However, this…
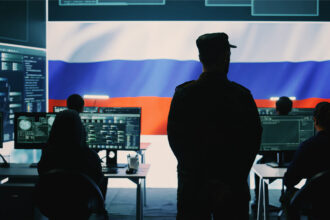
Hybrid threat: How drones over Poland translate into cyber risk
Analysis of Russian services' strategies and forecast of threats to the Polish IT sector and critical infrastructure.
The quantum time bomb is ticking. The problem is the present, not the future
Imagine assets that can be acquired at virtually no cost, but whose future value could be unimaginable. This…
Apple is betting on design. Is the iPhone Air a risky return to its roots?
After years of evolutionary changes and accusations of stagnation, Apple is returning to its roots, putting all its…
More than savings: The hidden revenue potential of CPaaS platforms
Contemporary communication platforms (CPaaS) are undergoing a quiet evolution, moving beyond their traditional role as a tool for…
The IT industry doesn’t need more leads. It needs better
In the IT industry, sales leads are no longer valuable in themselves. Their quality is becoming increasingly important—matching,…
Backup is not enough. How data immutability is redefining cyber security
The traditional approach to backup is no longer a sufficient guarantee of security. The key to survival is…
Organisational culture in an IT company – what leaders do, not HR
In technology companies, organizational culture is often reduced to values listed on a slide—trust, openness, responsibility. In practice,…
Beyond your own walls: How to secure the digital supply chain?
The days when cybersecurity ended at the edge of your own network are long gone, and today the…
SOC internal or external? A key decision for IT security
IT leaders face a strategic dilemma regarding the organization of cyber defense. They must decide whether it is…
An invisible front over the Baltic. How Russia’s electronic warfare is testing Europe’s resilience
The incident with Ursula von der Leyen's plane, whose navigation systems were deliberately disrupted during landing, was not…
Technological relic or ticking bomb? A simple guide to the security of legacy systems
Outdated technology in a company is a double-edged sword: on the one hand, it ensures the stability of…