Success for Poles in Apple Swift Student Challenge. Winning iOS apps
Two Polish students have joined the elite group of winners of this year’s Apple Swift Student Challenge 2026. Their winning…
Zero-day for $20. AI has just auctioned off cyber security
If you think artificial intelligence is mainly for writing LinkedIn posts and generating graphics, I have bad news:…
Ransomware in Q1 2026: Fewer gangs, more effective attacks
The cyberthreat landscape in the first quarter of 2026 underwent a significant transformation, resulting in a smaller number…
Why is a 10-character password not enough? Facts and myths
The effectiveness of modern authentication systems rarely depends on the mathematical perfection of algorithms; more often than not,…
Why are AI agents becoming the target of cyber attacks? Trend overview 2026
The shift from passive language models to autonomous AI agents radically expands the attack surface through vulnerability to…
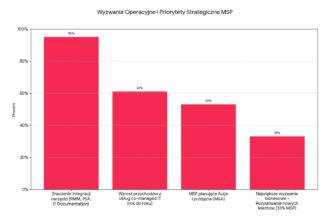
Challenges and priorities in the managed services market: Evolving from ‘handyman’ to business partner
The evolution of managed services is a journey from a reactive “handyman” to a proactive partner focused on…
14,000 cyber attacks in three months: Why is the 1970s protocol still a big risk for the industry?
Today’s industry relies on technology from the 1970s, which, due to a lack of encryption, has become an…
The printer as a ‘Trojan horse’ in the corporate network? How to turn the weakest link into a secure part of the IT ecosystem
Multifunction devices are advanced networked computers that, despite having constant access to corporate resources, often remain outside the…
Leaked controversial Claude Mythos model. Anthropic investigates security incident
Unauthorized access to the Claude Mythos model undermines the very foundation of Anthropic’s strategy, which is based on…
eAuditor V10 AI – scalability and flexibility in modern IT management
eAuditor is an advanced IT security and management platform that brings significant enhancements and new operational capabilities in…
SME cyber security 2026: How to build 360° resilience?
By 2026, a basic antivirus program on a computer will no longer be enough to effectively protect a…
Project Glasswing: How Anthropic wants to harness the power of its own artificial intelligence
The clash between exponential revenue growth and the self-imposed isolation of Claude Mythos—the most groundbreaking model—reflects Anthropic’s strategy,…
Attacks on US critical infrastructure. How Iran exploited flaws in the OT
The national security architecture faces a paradoxical challenge in which the most advanced defense systems are brought to…
How are NIS2 and DORA changing IT departments? New strategies in IT recruitment
Instead of worrying about empty chairs in IT departments, business leaders today must face a much more subtle…
Rowhammer attacks: is this the end of secure multi-tenancy? Why GPU-level isolation is now just an illusion
Trust in public cloud architecture is built on the foundation of impenetrable isolation, which, in the era of…
The CIO’s dilemma: How to reconcile speed of development with maximum protection?
The modern paradigm of technology management requires a shift away from a siloed view of infrastructure toward the…
Why is NIS2 a revolution in management, not just a change in IT?
The NIS2 Directive marks a landmark shift in cybersecurity, moving it from the realm of technical operations directly…
ISO 27001 in business: Why is certification an investment, not a cost?
The international ISO 27001 standard transforms information security from a technical requirement into a sophisticated business tool that…
Secure artificial intelligence in business – how to protect your business?
Although artificial intelligence is revolutionising Polish business, the stark disparity between the pace of innovation and the actual…
What is digital resilience and why does business need it?
Digitalisation has given organisations unprecedented speed, but at the same time has left them highly vulnerable to systemic…
How do you effectively protect your company data? Tips for World Backup Day
Although statistics on lost storage devices have improved over the last two decades, the physical loss of equipment…
Iranian hackers broke into the FBI director. Private data leaked
The hacking of FBI Director Kash Patel’s private email account by the Handala group is a demonstration of…