Izabela Myszkowska
IT’s hidden enemy. How is automation overcoming technology debt?
IT departments find themselves in the eye of the cyclone. Growing macroeconomic pressures, the explosion of remote and…
OT cyber security at the target of ransomware. How one mistake leads to production paralysis
The convergence of information technology (IT) and operational technology (OT) is accelerating, but its implementation is still fraught…
AI as a hacker? Researchers have investigated its capabilities and the results are worrying
Large language models can no longer just write lines and code, but can autonomously plan and execute complex…
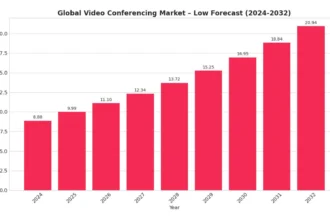
More than Zoom. The video conferencing market is growing by 10% a year. Who is making money from it?
Video conferencing, once a niche tool for global corporations, has become a cornerstone of business communication over the…
$30 billion in 3 months. Microsoft goes all out in the fight for AI
Microsoft has signalled that it is prepared to spend unprecedented amounts to dominate the era of artificial intelligence.…
A hidden feature in Nvidia chips? China speaks of ‘back doors’ and demands explanations
China's cybersecurity regulator (CAC) has summoned Nvidia for talks on the H20 chip, raising concerns about its security.…
Meta is earning crores from AI. There’s just one problem, and it’s costing billions
Meta Platforms is impressing with its financial performance, with revenue forecasts for the third quarter well ahead of…
Cloud in Europe: Between innovation and loss of sovereignty
Migration to the cloud promised companies flexibility and scalability they could not dream of in the era of…
The evolution of phishing: From fake invoices to job interview invitations
The job market has become a new hunting ground for cybercriminals. Instead of classic malware, they are reaching…
Microsoft’s shocking confession. One US law leaves them helpless
The issue of data sovereignty in the European Union is becoming increasingly important, and Microsoft' s recent statement…
Wi-Fi as a biometric tool: the potential and controversies of WhoFi technology
Ubiquitous video surveillance, cameras present in almost every public space - this is our reality today, for which…
VMware changes – Broadcom restricts access to security updates
Following the acquisition of VMware by Broadcom, customers with perpetual licences are facing a new and uncertain reality.…
Palo Alto preparing the acquisition of the decade? They’ve confirmed one purchase, with another giant on target
Focus on AI in cyber security drives acquisition market. Palo Alto Networks has officially confirmed the finalisation of…
A boom that has spun out of control. China is centralising computing power
After three years of rapid expansion of its digital infrastructure, China is taking steps to clean up its…
OpenAI is preparing the GPT-5 for August. What does the new model change?
OpenAI is preparing for the launch of GPT-5, a new version of its flagship AI model. The Verge…
Behind Nvidia’s back. A quiet war for dominance in the AI server market
The AI revolution has the face of Jensen Huang and the NVIDIA logo, but behind the scenes of…
The more tools, the worse? The cyber security paradox that is destroying businesses
Companies are investing in dozens of tools to protect their growing infrastructure. However, this intuitive action creates a…
China’s AI chip black market a challenge for Nvidia and the US
A new report from the Financial Times sheds light on the illegal market for artificial intelligence chips that…
8 overrated technologies
In theory, everything looked beautiful. Generative artificial intelligence was supposed to automate entire business processes, agent-based AI was…
MSP 2.0: How managed service providers are transforming into strategic partners in cyber security
For years, managed service providers(MSPs) were seen as external IT teams - helpful but on the sidelines. Today,…
From annoying bot to empathetic assistant: how AI is learning to be human
For years, chatbots had one task: to solve a case cheaper and faster than a human. In practice,…