Japan sets up task force against Mythos AI threats
Anthropic’s revelation that the Mythos model is capable of instantly compromising critical operating systems triggered an immediate response at the…
Attacks on US critical infrastructure. How Iran exploited flaws in the OT
The national security architecture faces a paradoxical challenge in which the most advanced defense systems are brought to…
Physical AI: A groundbreaking trend in the evolution of artificial intelligence in the real world
Przejście od czysto kognitywnych modeli językowych ku Physical AI wyznacza nowy horyzont, w którym sztuczna inteligencja opuszcza bezpieczne…
OT cyber security, a new pillar of profitability for energy companies
The energy sector has finally abandoned the illusion of stability, becoming an arena where geopolitical interests intersect with…
A factory is not an office. Why do IT methods fail in manufacturing security and how to do it right?
Many industrial companies still labor under the misconception that traditional IT security measures are sufficient to protect critical…
OT cyber security at the target of ransomware. How one mistake leads to production paralysis
The convergence of information technology (IT) and operational technology (OT) is accelerating, but its implementation is still fraught…
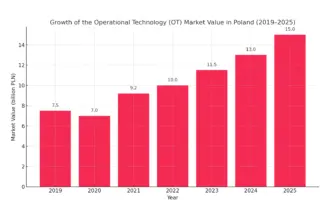
Operational transformation: How the OT market is growing in Polish industry
Operational technology (OT) - i.e. industrial control, automation and critical infrastructure systems - has become a pillar of…