The US Department of Justice, in cooperation with law enforcement agencies from Germany and Canada, announced the dismantling of the infrastructure of four powerful botnets: Aisuru, KimWolf, JackSkid and Mossad. These networks have infected more than 3 million devices worldwide, becoming one of the most disruptive tools in the hands of cybercriminals
This hit is not only an operational success, but a clear signal to the technology sector. These botnets specialised in Distributed Denial of Service (DDoS) attacks, paralysing the servers of global institutions, including those of the US Department of Defense. They primarily exploited poorly secured Internet of Things (IoT) devices – from home routers to CCTV cameras. There is a lesson in this for business: security vulnerabilities in simple consumer devices are now becoming weapons aimed at critical state and corporate infrastructure.
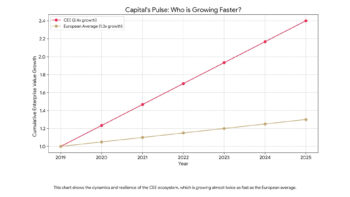
The style of the operation is reminiscent of modern crisis management in the Big Tech sector. Indeed, an unusual alliance was brought together to fight criminal groups. In addition to federal agents and Europol (the PowerOff team), nearly two dozen technology giants, including Amazon Web Services, Google, PayPal and Nokia, were involved. Such a broad coalition of the public and private sectors demonstrates that in an age of distributed threats, no single institution can guarantee network security alone.
The operators of the crashed networks were not limited to sabotage. Investigative documents point to attempts to extort ransoms from victims, in line with the trend towards the commercialisation of cybercrime. While the elimination of Aisur or Mossad is a severe blow to the criminal ecosystem, experts warn against excessive optimism. Botnet infrastructure tends to regenerate quickly and the low digital hygiene of IoT device users still leaves the door open for new threats.