Back to School, Back to Risk: Are schools ready for digital risks
With the first bell ringing, millions of students log into school systems, beginning a new year full of…
Akamai Technologies warns: 4-step blackmail defines the new face of ransomware
Double extortion in ransomware attacks is no longer enough for cybercriminals, who are escalating to a four-phase blackmail…
The lost innocence of the web: the story of the first great cyber attack
On November 2, 1988, a program consisting of just 99 lines of code, written by a single student,…
Phishing training is losing its lustre: why effectiveness is lower than the market promises
The largest study to date on the effectiveness of phishing training shows that the effects of employee education…
Clickjacking as part of the attack chain: an underestimated threat in security architecture
Clickjacking has remained on the periphery of security departments' attention for years - regarded more as a threat…
Why every cable in a factory today is a potential entry point for a hacker
Just a decade ago, the industrial production line was a closed world. Machines ran on isolated networks and…
The cyber security market is not slowing down. Here’s what’s driving it
Global spending on cyber security is growing at a double-digit rate. According to the latest forecasts from analyst…
The biggest security gap in AI is not the code. It’s the people
In 2023, a quiet drama unfolded in the corridors of tech giant Samsung. It was not a hacking…
Second-hand ransomware. How copying code lowers the barrier to entry to cybercrime
If cybercrime had its own GitHub, Nitrogen ransomware and LukaLocker would be its popular forks. An increasing number…
ReVault: Five serious security vulnerabilities in over 100 Dell laptop models
Cisco Talos has disclosed five serious vulnerabilities in the Dell ControlVault3 firmware and associated Windows APIs. Collectively named…
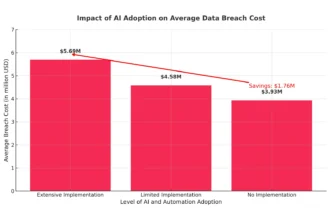
AI in cyber security, or how to save $1.76m and reduce attack response by 108 days
Every IT leader and security director knows this scenario all too well: the endless stream of security alerts,…
Technological arms race – who is using and who is fighting deepfake?
The rise of deepfake fraud is accelerating, forcing companies into a technological arms race. As artificial intelligence becomes…
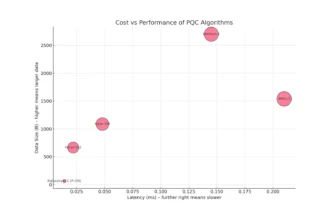
Post Quantum Cryptography: Business implications of algorithm choice
Today's digital economy rests on an invisible but fundamental pillar: public key cryptography. Algorithms such as RSA and…
OT cyber security at the target of ransomware. How one mistake leads to production paralysis
The convergence of information technology (IT) and operational technology (OT) is accelerating, but its implementation is still fraught…
AI as a hacker? Researchers have investigated its capabilities and the results are worrying
Large language models can no longer just write lines and code, but can autonomously plan and execute complex…
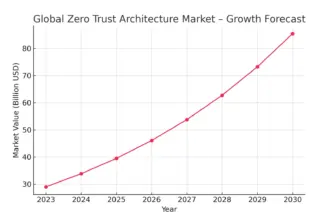
An investment that pays off – implementing Zero Trust architecture
Traditional security models are no longer effective. The 'castle and moat' concept - assuming that everything inside the…
The evolution of phishing: From fake invoices to job interview invitations
The job market has become a new hunting ground for cybercriminals. Instead of classic malware, they are reaching…
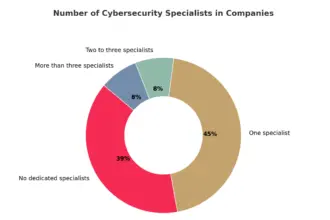
Poland’s alarming skills gap. Why are we such an easy target for hackers?
Poland's economy is at the heart of a digital paradox. On the one hand, the country is dynamically…
The more tools, the worse? The cyber security paradox that is destroying businesses
Companies are investing in dozens of tools to protect their growing infrastructure. However, this intuitive action creates a…
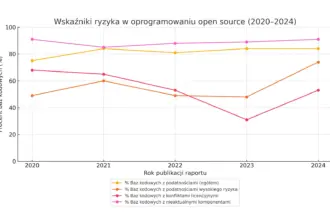
The Open Source Paradox – How innovation became the biggest threat to business
Oprogramowanie open source stało się fundamentem współczesnych aplikacji – odpowiada dziś średnio za 77% całego kodu w rozwiązaniach…
Cyber insurance is not enough. Why don’t policies cover real losses after an attack?
More and more companies are investing in cyber insurance, seeing it as the last line of defence against…