Public Wi-Fi versus your finances: A guide to online security
Using public Wi-Fi networks has become a symbol of modern flexibility, offering invaluable convenience in everyday work. However,…
Anatomy of a zero-day attack: How hackers exploit unknown vulnerabilities and how to defend against it?
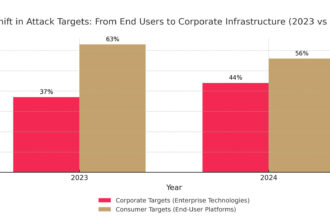
Attackers have changed their strategy, targeting not millions of users, but the heart of corporate infrastructure through unknown…
They sold LinkedIn data for $15,000. The backstory of the lawsuit against ProAPIs
LinkedIn has taken legal action against ProAPIs, accusing it of creating a vast network of bots to illegally…
Renault: Customer personal data stolen in cyber attack on third-party company
Renault UK has confirmed a customer data breach following a cyberattack on one of its external suppliers. The…
Pact with the devil or deal of the century? Hollywood and OpenAI sit down at the table on Sora
OpenAI is preempting potential legal disputes over its Sora video generation tool by offering film studios and copyright…
Cyber attack on Salesforce customers. Hackers claim to have taken over one billion records
A cybercriminal group calling itself “Scattered LAPSUS$ Hunters” claims to have stolen nearly a billion records belonging to…
Apple is betting on smart glasses. Vision Pro loses priority
Apple is changing its strategy in the mixed reality segment, suspending development of the new version of the…
AI in everyday life: 5 applications you had no idea about
Artificial intelligence has become a quiet but ubiquitous architect of our everyday lives, operating far beyond commonly known…
Generation Z raised on the internet most likely to fall for phishing
Contrary to popular belief, the generation raised in the digital world turns out to be the weakest link…
AWS and NBA join forces: data, AI and new experiences for fans
Amazon Web Services and the NBA are strengthening their partnership by launching a new platform called Inside the…
From server rooms to AI gigafactories: the decade that changed data centres
Just a decade ago, data centers served as the invisible backbone of business—they ran applications and stored data,…
Machine learning after 60 years – from a game of checkers to a key tool in business IT
Machine learning has been around for over 60 years, but only today has it become one of the…
KPMG: only 40% of leaders feel their companies are adequately protected
Polish companies are investing more and more in cybersecurity, expanding their teams and increasing their budgets, but at…
AI is not enough. Marketing discovers the gravity of data
Digital marketing is entering an era where data is becoming as compelling as artificial intelligence itself. The Snowflake…
Cyber attacks on industry are increasing by 30% a year. Companies need to act strategically
The manufacturing industry has become one of the main targets of cybercriminals, and the scale of attacks is…
Cloud costs vs edge costs – the illusion of cheap IT
For years, the cloud has been considered a cheap and flexible response to business needs, but in practice…
Click and regret: the dark side of AdTech
Cybercriminals are increasingly operating in broad daylight, exploiting the advertising industry's infrastructure rather than hiding in the darknet.…
Canon enters 3.2m market with new Colorado XL series
Canon enters the 3.2-meter wide format printing market with the launch of its new modular Colorado XL series…
Why databases are still the Achilles heel of DevOps
DevOps has accelerated application development and revolutionized the way applications are deployed, but manual processes and the risk…
AI trapped in déjà vu: companies are repeating the mistakes of RPA and BPM again
Generative artificial intelligence is entering the business world at an impressive pace, and companies are racing to harness…
Fire at government data centre paralyses South Korea
South Korea, a global leader in digitalization, is grappling with the paralysis of public services following a fire…